In probably the shortest time ever between this post and the last one, it’s time to look back on the Cyber Security Challenge Masterclass that happened last week.
On the morning of the 11th, a few hours before were going to arrive at the hotel for introductions etc ahead of the main competition on the Thursday, I was asked if I wanted to appear on ITV’s Good Morning Britain. So I hopped on an earlier train and arrived at HMS Belfast. The organisers were setting up all the networks etc. for the next day of competitions so with some not very convincing acting we pretended to save London from a major attack (the video is here for those who are interested).
After a quick check-in in an amazing hotel just by tower bridge, we were off to the BT centre by St Paul’s. Here we had ‘networking’ and talks, including one by some school children about the new computer science GCSEs. The lasting memory of that night though is the lack of proper food!
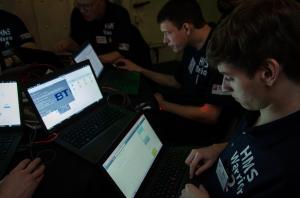
Thursday 12th started early, however these early starts were rewarded with some great sunrises. After some short health and safety and introductory talks we were sat on our tables with our laptops and told to map out the network. The competition structure was a combination of ‘stop them’ and ‘capture the flag’, however there were also negative flags. Each team was given an FTP server where they could share information but it also contained password protected zip files, most of which were released to us over the course of the competition. During this time we found a flag (an empty file with the file name CSC_FlAG_xxxxx where xxxxx was a number that is unique to the flag) in one of the zip files. We found out much later that this was a negative flag, the only one that any team found! However, soon after that we were given access to one that gave us a network map of the ship and some network traffic captures, one outside the network as a pcap and one inside as a netflow. This told us that the network had a subnet that contained a mail server, a DNS server and a sys log server. The syslog server had a PPoE connection to ‘gunnery’ where the gun controls were located.
Quite a lot of the challenge consisted of persuading the people who set the challenge from GCHQ to give us access to more and more servers based on the evidence provided in some network packet snapshots that showed SSH traffic leaving for the internet. We had to show both the internal netflow records pcap file agreed with each other. Having worked out the route onto the mail server and then the syslog server we started to tackle the gunnery server. My main role during the latter part of the day (when I’d lost my voice!) was to trace the hacker that had infected the systems. We knew that they had downloaded some prefabbed exploit from pastebin and I used that to track him back to his flat, which was good fun. The final part of the day was being put up against people from CERT UK, GCHQ, NCA, Bank of England and others in a huge grilling that was both very difficult and also one of the most rewarding parts of the whole day. This really shows that it’s not just technical skills that are put to the test but ‘softer’ skills also. That night there was a bar aboard the ship, however it turns out that the organisers staffing the bar where in fact there to try and catch people leaking secrets! After that it was right back to the hotel, early start the next day!
On the 13th we arrived bright and early to continue our challenge. After a quick brief we were led outside for a ‘networking’. However, it turned out the insider was part of the challenge. Cue the NCA and PGI turning up on a speedboat arresting him, which was very funny. Back inside and our team was feeling a bit depressed as we were bottom of the flag leaderboard and then we were turfed out for our SCADA challenge. This was run by Airbus Group and involved an hour try and break through a series of servers controlling a smart grid, smart factory and a water purification plant. The setup was very realistic (abet with some glaring vulnerabilities that you would hope wouldn’t find in the real world!) and although we didn’t stop any of the plants working we were very close to the water plant (finally, my Windows knowledge came in use towards the end of the last day!). Next we had our second grilling by the panel, this time it went much better! Pretty much straight after that it was all over and we retired to the hotel while the assessors made their judgements.
That evening at the hotel was the final awards dinner, a more formal event and the culmination of the years activities. Various awards were given out including a clean sweep for overall winner, runner up, best team and best SCADA challenge for team HMS Belfast. Lots of interesting people were met and prizes dished out, everyone was invited to GCHQ in May and I received an invitation to an IAAC meeting and a CompTIA Security+ voucher! A late night was then had in the hotel bar…
All in all the experience was very rewarding and well worth doing, I hope this provides a very brief overview of what masterclass is like. Hopefully I’ll be doing something similar at the next masterclass in November!



Comments are closed, but trackbacks and pingbacks are open.